What is a Time-based One-time Password (TOTP)?
A standardized algorithm that uses the device time as an input and generates unique numeric passwords. A Time-based One-Time Password (TOTP) serves as a form of two-factor authentication (2FA). Other terms for TOTP include app-based authentication, software tokens, or soft tokens. RFC 6238 defines this algorithm. When used as a second factor, the TOTP increases account security.
Authentication apps support the TOTP standard.
In addition to SMS, voice, email, and push channels, the Twilio Verify API supports TOTP authentication.
By requiring two types, or factors, of authentication, 2FA adds an extra layer of account protection. This can be knowledge (something a user knows, like a password) and possession (something the user has, like a phone). One-time passwords like TOTP are a common possession factor.
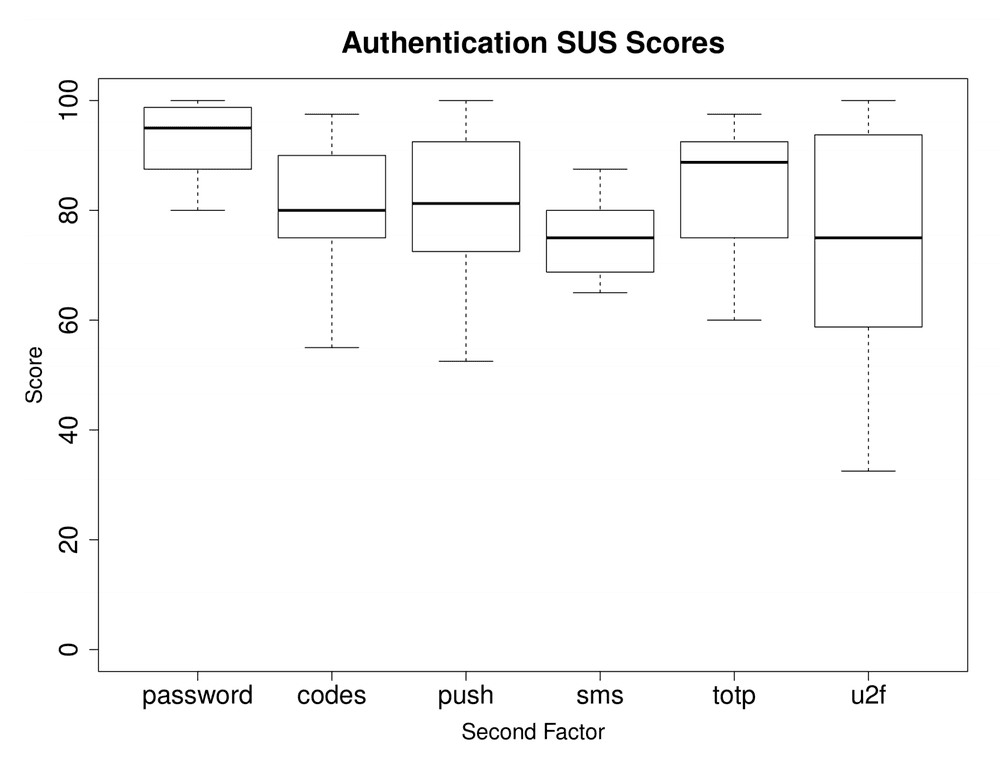
A 2019 study about the usability of 2FA methods found that TOTP had the highest usability score of the various second factors tested. This study explains that TOTP is both viable and user preferred.
One-time password options can also use a Hash-based Message Authentication Code (HMAC). RFC 4226 defines the HOTP standard.
TOTP bases its approach on the HMAC-based One-Time Password (HOTP) algorithm. While both methods use a secret key as one of the inputs, TOTP uses the system time for the other input, and HOTP uses a counter. This counter increments with each validation. With HOTP, both parties increment the counter and use that to compute the one-time password.
Most consumer authenticator apps implement the TOTP standard.
Defined in RFC 6238, the TOTP algorithm takes a shared secret key and the device time as inputs. For the shared secret key, the algorithm uses a form of symmetric key cryptography. Both parties use the same key to generate and validate the token.
The TOTP algorithm takes the device time and a stored secret key as inputs. Generating or verifying a token doesn't require internet connectivity, so a user can use TOTP through an app while offline. The following diagram shows how both parties calculate the passcode.
While SMS has built 2FA adoption, TOTP has several benefits including:
- Offline support
- Registration without providing personally identifiable information (PII)
- Standardized authentication solution
- Software-based
- Independent of carrier fees or telephony access and deliverability
- Faster average time to authenticate
- Increased security
- The TOTP-required secret key gets shared once.
- TOTP doesn't need a carrier network, which reduces the attack surface.
- TOTP has stronger proof of possession than SMS as one can access it only from one place.
To give users a choice of options, most Twilio customers implement multiple forms of 2FA. Twilio Verify also supports other channels, including push, voice, and email.