5 reasons SMS 2FA isn't going away
Time to read:

Every security solution is a delicate balance between protecting some kind of value and providing usable access to the right people. We're all constantly evaluating the tradeoffs and calculating risk in order to find the right balance of security and usability. When there's more at stake, people are willing to add additional friction and protections. In the physical world that could mean a personal apartment has a simple deadbolt while a jewelry store invests in an alarm system.
For online business, SMS authentication has long been a popular choice for securing consumer accounts. It's an easy and familiar channel to deploy and SMS two factor authentication (2FA) usage has even grown 9% in the last two years. While the SMS channel has legitimate security concerns, businesses should consider their threat model and offer a spectrum of 2FA options. Offering more secure channels like authenticator apps and push authentication is especially important when you're protecting high value targets like a bank account or email.
Why has SMS remained so popular despite its flaws? When is it not enough?
1. Passwords suck
We've been using passwords as the de-facto standard for authentication since the internet started. But humans are forgetful, so we use short, memorable passwords that can be guessed or brute-forced. I wouldn't be surprised if M@rch2021! is a common choice right now.
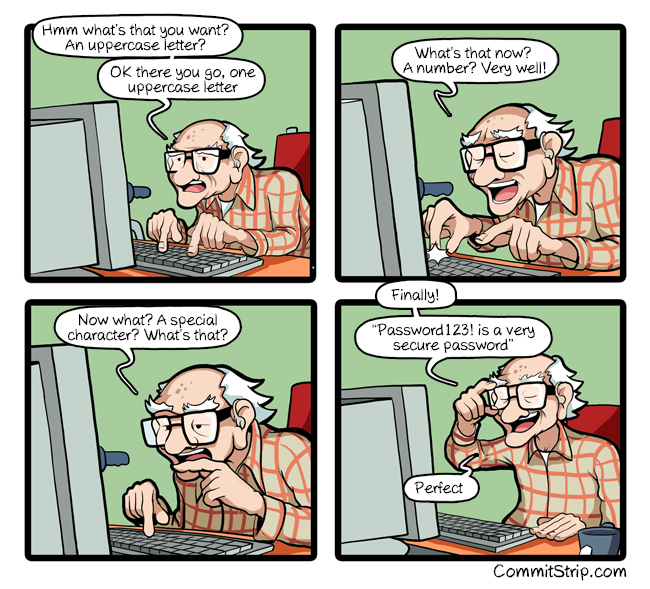
The website haveibeenpwned.com collects credentials seen in data breaches and proves how common simple, guessable passwords are. For example, the password 123456 has been seen in data breaches over 24 million times. To make matters worse, a 2019 Google study shows that 64% of people admit to reusing passwords across multiple sites. This is a problem because even if someone has a complex password, if they’re reusing it for many sites, a data breach at MySpace or Adobe could lead to the user’s account getting breached on your company’s site through a process known as credential stuffing.
Password managers help, but less than 25% of Americans use one. So the industry started introducing additional security measures.
2. Most people can receive text messages
In order to supplement the insecurity of passwords, many companies started introducing 2FA, using something you know (password) and something you have (phone). Receiving a one-time passcode over a text message can protect an account if the first factor (password) is compromised. And since we established that passwords can be compromised, this is pretty great news.
96% of Americans have a mobile phone capable of receiving text messages. While the number of smartphone users is rapidly increasing, SMS does not require an additional app download in order to opt into an additional security measure.
The ease of onboarding with SMS can help make sure people enable a second factor.
3. SMS 2FA works
The state of online security is constantly improving and the industry is always adapting to accommodate emerging technology. But even companies like GitHub who implement a wide variety of 2FA options still allow SMS 2FA as an option. Importantly, GitHub doesn't force users to use SMS, but leaves it as an option for people who might value convenience over the additional protections of something like TOTP or WebAuthn.
Google research also shows that SMS is still an effective form of authentication, helping "block 100% of automated bots, 96% of bulk phishing attacks, and 76% of targeted attacks".
4. 2FA is only useful if users opt in
While companies can require that employees enable 2FA, most consumer applications don't enforce 2FA. Onboarding is incredibly important because offering secure authentication channels isn't good enough if no one uses them. SMS 2FA is one of the lowest friction ways of adding 2FA to an account: in a research study users were able to set up the factor on average 2.6 times faster than an authenticator app. Unfortunately, many users won't take the time to download an additional authenticator app. This is also why I don't expect WebAuthn to take off until platform authenticators are widely available.
A 2019 study on 2FA usability found that only 29% of people thought the inconvenience of 2FA was always worth the security tradeoff. As one participant observed: "I just don’t think I have anything that people would want to take from me, so I think that’s why I haven’t been very worried about it".
To offset the time investment, you can incentivize 2FA like Fortnite did by enabling in-app rewards for gamers.
5. NIST says SMS 2FA is ok
The National Institute of Standards and Technology (NIST) debated deprecating SMS as a 2FA channel back in 2016 but after requesting public commentary ultimately kept SMS as a recommendation for a second factor. NIST acknowledged that "Leveraging a SMS to mobile as a second factor today is less effective than some other approaches—but more effective than a single factor. This balancing act is difficult and inherently imperfect". They do discourage using VoIP numbers, which can't prove possession of a device. Read more about NIST's recommendations for out-of-band authenticators in special publication 800-63b.
No security solution is perfect
SMS wasn't built to be a security tool and ended up as one anyway. But attacks require varying levels of skill and money to execute.
A security researcher named Roger Piqueras Jover analyzed SIM swap attacks and found that while the attack is cheap, it's time consuming and leaves a trace. "Despite being a widely acknowledged security risk in America and Europe, [SIM swaps are] a much mitigated threat in African nations." A bank in Mozambique can check for recent SIM swap activity with a cellular operator, a strategy that has "reduced SIM swap-based banking fraud to nearly zero overnight." This is why Twilio is investing in solutions to help businesses defend SIM swap and account takeover.
The same research found that while an SS7 attack is fast, it's expensive and it requires specialized knowledge of SS7 protocols and access to the SS7 network. Recent reports of message forwarding services that can be abused to re-route messages to an attacker are concerning, but security researchers are actively exposing this abuse and have built tools to help detect this type of attack.
Most of these weaknesses would be exploited with targeted attacks, where you would have a specific victim in mind. "If your threat model is such that you’re in the public eye (journalist, activist, etc) then this is even more important for you — folks in the public eye are more likely to be targeted by criminals" social engineering expert Rachel Tobac tweeted this week.
A huge mitigation businesses can and should offer their customers is the option to enable stronger methods of authentication for the people who might be a target. Depending on the service, additional protections could be required based on a threshold for account value like financial balance or number of social media followers.
When SMS 2FA isn't enough
Every business has a unique threat model, so consider what your business is protecting and how your users might be targeted. Add additional security for high value accounts—think financial accounts and email—and high value targets—like celebrities, elected officials, or activists—with:
- Authenticator Apps (TOTP) like Authy.
- Push authentication, especially for business with a large number of mobile application users.
- Services like Sift to help detect fraud in the background.
- WebAuthn, which is still new but a promising password replacement.
- Email, which has different security tradeoffs but may be worth considering in addition to other channels and signals.
An important part of every authentication system is account recovery, so if you do offer SMS 2FA, consider how you want to use it in case of a lost password. We recommend using SMS in combination with backup codes or other possession channels to add even more protection for those accounts/users. For additional safeguards, consider adding forced waiting periods and email notifications that a recovery is in progress. For more recommendations, including how to balance account recovery with support costs, check out this talk on designing customer account recovery in a 2FA world.
There's no one size fits all solution here, but I encourage you to delight your security conscious users with secure channels and provide flexible options for the rest. Because like the security researcher Cormac Herley says, "when we exaggerate all dangers we simply train users to ignore us."
Related Posts
Related Resources
Twilio Docs
From APIs to SDKs to sample apps
API reference documentation, SDKs, helper libraries, quickstarts, and tutorials for your language and platform.
Resource Center
The latest ebooks, industry reports, and webinars
Learn from customer engagement experts to improve your own communication.
Ahoy
Twilio's developer community hub
Best practices, code samples, and inspiration to build communications and digital engagement experiences.

