Fraud & Abuse Response Guide
This guide is designed to help you quickly identify, contain, and remediate fraud or abuse on your Twilio account. It provides a practical phase-based approach you can follow when suspicious activity occurs, so you can act fast and reduce impact.
At Twilio, we view security and fraud prevention as a shared responsibility. While our internal systems proactively monitor for anomalies to provide a fast turnaround for intervention, no automated system can catch everything. The most resilient applications pair Twilio's built-in protections with custom Usage Triggers and proactive monitoring.
We know that a service interruption is the last thing you want. However, if our systems flag activity that looks like a serious threat, we might step in to protect your account. This can usually look like placing restrictions, deprovisioning phone numbers, suspending your campaigns, or even suspending your affected accounts.
If your account has been restricted, don't panic. We want to help you get back online as much as you do. Following the containment steps in this guide is the fastest way to secure your integration and get back to building.
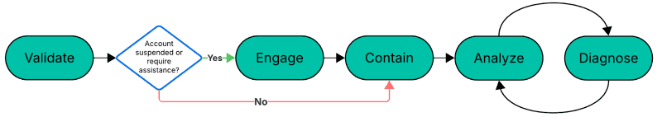
Fraud response isn't always linear, but speed is your best friend. While you might jump between these steps, your primary goal is to reach the 'Contain' phase as fast as possible.
Before you pull any levers, confirm what you're seeing. Identify whether you're facing an Account Takeover (ATO), Artificially Inflated Traffic (AIT/SMS Pumping), or a smishing/vishing campaign. Confirming the "flavor" of the fraud ensures you apply the right fix. Here are some of the most common types of fraud:
- Account Takeover (ATO) – This is a breach of access to your Twilio account(s). Look for unrecognized login activity, unexpected changes to your account credentials, or new API keys that your team didn't generate.
- Artificially Inflated Traffic (AIT) – A broad category of fraud involving artificially generated usage designed to increase traffic and cost. SMS pumping is a common (but not the only) form of AIT, and typically appears as an unexpected, high-volume surge of traffic (usually messages) targeted at specific country prefixes (often high-cost or premium routes). This is typically driven by bots exploiting a signup form or a verification flow.
- Smishing/Vishing – This is a breach of trust. This involves malicious links or deceptive voice calls originating from your Twilio numbers, often aimed at tricking your end-users into giving up their own private info.
While we recommend prioritizing Phase 3 (Contain) to stop the immediate impact, our team is here to help. You should reach out to Twilio Support if:
- Twilio proactively restricted your account due to fraud. We'll work together to verify containment before restoring service.
- You've followed the self-service steps in this guide but still need help auditing the affected accounts or identifying the root cause.
- You want a second pair of eyes to ensure your containment strategy is airtight.
To help us help you faster, when you open your ticket with Twilio Support, share everything you've found. Information like Account SIDs, specific phone numbers, targeted prefixes, or suspicious timestamps make a huge difference. The more data you provide, the faster we can get to the bottom of the incident.
Do not wait for a response from Twilio Support to start this phase. This is where you take immediate action to cut off the attacker's access. Whether it's rotating API keys, updating Geo-Permissions, or rate-limiting your forms, the goal is to stop the financial and reputational impact now.
Once you have successfully completed the containment phase, gather the facts to answer: "How did this activity occur?" During this phase, you will perform a deep dive into your Twilio usage logs and application records to assess the full scope of the incident. By documenting the impact (including affected subaccounts, total traffic volume, and associated costs) you create the data set necessary to understand the breach and begin a full recovery.
This is where you answer the critical question: "Why did this activity occur?" You will identify the specific reasons the fraud was possible and how existing security controls were bypassed. By synthesizing the data gathered during the Analyze phase, you can build a comprehensive timeline and define a plan for long-term security improvements.
In some cases, you may be required to close out the investigation with an RCA document. This document should detail the timeline of events, your investigative findings, and the specific recommendations you are implementing to harden your security posture.