Authy One-Time Passwords (OTP)
Warning
As of November 2022, Twilio no longer provides support for Authy SMS/Voice-only customers. Customers who were also using Authy TOTP or Push prior to March 1, 2023 are still supported. The Authy API is now closed to new customers and will be fully deprecated in the future.
For new development, we encourage you to use the Verify v2 API.
Existing customers will not be impacted at this time until Authy API has reached End of Life. For more information about migration, see Migrating from Authy to Verify for SMS.
Before sending a One-Time Password:
- Create an Authy Application (see Applications documentation)
- Create a User (see Users documentation)
Once a user has been registered with your Twilio Authy application and receives an AuthyID, you can now implement 2FA, passwordless login or protect an in-application high-value transaction. Using the Authy API, you can send one-time passwords over voice or SMS channels.
Users can also install the free Authy app or use our SDK to generate offline TOTP codes (soft tokens). Soft tokens do not require wireless connectivity to issue and verify.
The Authy API is used to verify a user has access to the right phone number (for SMS and Voice channels) or has access to the right trusted device (for TOTP via the Authy App or use of the SDK).
Twilio's Authy API follows the algorithms described in RFC 6238 and RFC 4226 to generate TOTP (Time-Based One-Time Passwords) passwords. It is also possible to use your own hardware tokens, please contact us for information on how to enable this type of 2FA.
When you call the API to start either an SMS or voice-based authentication, it automatically checks to see if that user has previously downloaded the Authy app or has an app installed that uses our SDK. If the user has the Authy App, by default, the API will not send the 2FA code via SMS or voice. Instead, a push notification will go to the device , prompting the user to start their app to get the code.
If a user has no record of installing a device, then the API will continue to send the code via SMS or voice. You can override the default behavior to force the sending of code via SMS or voice every time. This is a useful override if a user is specifically selecting "Send SMS" or "Get code via voice call" in your application UI.
For information on timing and other constraints like rate limiting, see our two-factor authentication best practices.
GET https://api.authy.com/protected/{FORMAT}/sms/{AUTHY_ID}
| Name | Description |
|---|---|
FORMAT String | The format to expect back from the REST API call. json or xml. |
AUTHY_ID Integer | The Authy ID of the user to send an SMS TOTP. Create an Authy ID by registering a user. Note that password delivery may be upgraded to use the Authy application; see response parameters below. |
| Name | Description |
|---|---|
force Boolean (optional) | Default is false. Set to true to send one-time passwords over the SMS channel even if the user has an Authy or SDK enabled app installed. Configure default behavior in the console. (🏢 not PII ) |
action String (optional) | The optional action or context we are trying to validate. (🏢 not PII ) |
action_message String (optional) | Optional message for the specific action. (🏢 not PII ) |
locale String (optional) | The language of the message received by user. If no locale is given, Twilio will try to autodetect it based on the country code. English is used if no locale is autodetected. More details below (🏢 not PII ) |
| Name | Description |
|---|---|
success Boolean | Returns true if the request was successful. (🏢 not PII ) |
message String | A message indicating what happened with the request. (🏢 not PII ) |
cellphone String | The country code and last two digits of phone number used to send the message with the rest obfuscated. (🏢 not PII ) |
ignored Boolean | True if we detected an Authy or SDK enabled app installed and we upgraded the OTP delivery channel from 'SMS' to Push Notification. Authy or SDK users are redirected directly to the requested token. (🏢 not PII ) |
device String | The type of the last device used by the user. This is only returned when we upgraded delivery from SMS. (🏢 not PII ) |
Supported languages are: Afrikaans (af), Arabic (ar), Catalan (ca), Chinese (zh), Chinese (Mandarin) (zh-CN), Chinese (Cantonese) (zh-HK), Croatian (hr), Czech (cs), Danish (da), Dutch (nl), English (en), Finnish (fi), French (fr), German (de), Greek (el), Hebrew (he), Hindi (hi), Hungarian (hu), Indonesian (id), Italian (it), Japanese (ja), Korean (ko), Malay (ms), Norwegian (nb), Polish (pl), Portuguese - Brazil (pt-BR), Portuguese (pt), Romanian (ro), Russian (ru), Spanish (es), Swedish (sv), Tagalog (tl), Thai (th), Turkish (tr), Vietnamese (vi). We support the format country-region as described in IETF's BPC 47. If no region is given (or supported), there will be a default by country.
1# Download the SDK from https://github.com/twilio/authy-python2from authy.api import AuthyApiClient34# Your API key from twilio.com/console/authy/applications5# DANGER! This is insecure. See https://twil.io/secure6authy_api = AuthyApiClient('api_key')78sms = authy_api.users.request_sms(authy_id)910if sms.ok():11print sms.content
Output
1{2"success":true,3"message":"SMS token was sent",4"cellphone":"+1-XXX-XXX-XX02"5}
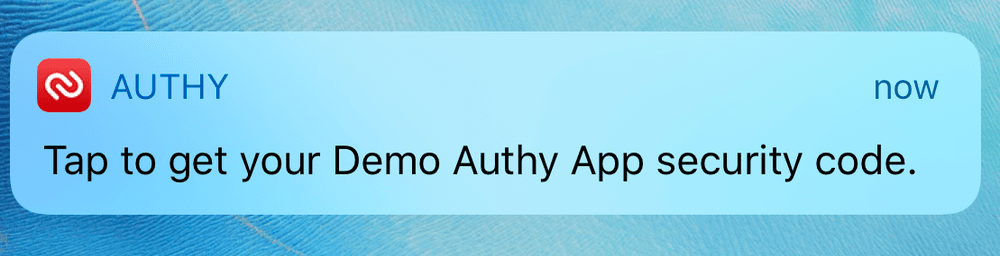
If the user has the Authy App, by default, the API will not send the 2FA code via SMS or voice. Instead, a push notification will go to the device, prompting the user to start their app to get the code. The user's notification will look like this:
If the user has the Authy app installed the API response will look like this:
1{2"message": "Ignored: SMS is not needed for smartphones. Pass force=true if you want to actually send it anyway.",3"cellphone": "+1-XXX-XXX-XX02",4"device": "android",5"ignored": true,6"success": true7}
You can override this behavior and force sending an SMS or Voice call. This is a useful override if a user is specifically selecting "Send SMS" or "Get code via voice call" in your application UI.
1# Download the SDK from https://github.com/twilio/authy-python2from authy.api import AuthyApiClient34# Your API key from twilio.com/console/authy/applications5# DANGER! This is insecure. See https://twil.io/secure6authy_api = AuthyApiClient('api_key')78sms = authy_api.users.request_sms(authy_id, {'force': True})910if sms.ok():11print sms.content
Output
1{2"success":true,3"message":"SMS token was sent",4"cellphone":"+1-XXX-XXX-XX02"5}
Optionally, you can limit a specific token to a single action, for example coupling a one-time password to a specific login request or transaction. Most implementations will not need this feature.
You can pass action= and action_message= (optional) to send a code that is only valid for the given action. This is useful if you require codes to perform different actions on your app, for example, you can pass action=login&action_message="Login code"when sending a login code.
When using this option you must pass the same action when verifying the code.
Warning
- Sending an SMS with custom actions will always send the SMS even if the
user has the Authy app installed. Sending
force=trueisn't necessary. - Codes generated through regular SMS and the Authy app won't work when sending the custom actions parameters to the verify endpoint.
- Custom actions isn't supported for voice calls.
1# Download the SDK from https://github.com/twilio/authy-python2from authy.api import AuthyApiClient34# Your API key from twilio.com/console/authy/applications5# DANGER! This is insecure. See https://twil.io/secure6authy_api = AuthyApiClient('api_key')78sms = authy_api.users.request_sms(9authy_id,10{'action': 'login', 'action_message': 'Login code'})1112if sms.ok():13print sms.content
Output
1{2"success":true,3"message":"SMS token was sent",4"cellphone":"+1-XXX-XXX-XX02"5}
For users that don't own a smartphone or are having trouble with SMS Tokens, Authy allows you to use phone calls instead. Like SMS, by default this call will be ignored if the user is using the Authy Mobile app. You can override the default behavior with the force parameter.
GET https://api.authy.com/protected/{FORMAT}/call/{AUTHY_ID}
| Name | Description |
|---|---|
FORMAT String | The format to expect back from the REST API call. json or xml. |
AUTHY_ID Integer | The Authy ID of the user to send an SMS TOTP. Create an Authy ID by registering a user. Note that password delivery may be upgraded to use the Authy application; see response parameters below. |
| Name | Description |
|---|---|
force Boolean (optional) | Default is false. Set to true to send one-time passwords over the Voice channel even if the user has an Authy or SDK enabled app installed. Configure default behavior in the console. (🏢 not PII ) |
action String (optional) | The action or context we are trying to validate. (🏢 not PII ) |
action_message String (optional) | Message for the specific action. (🏢 not PII ) |
locale String (optional) | The language of the message received by user. If no locale is given, Twilio will try to autodetect it based on the country code. English is used if no locale is autodetected. More details above. (🏢 not PII ) |
| Name | Description |
|---|---|
success Boolean | Returns true if the request was successful. (🏢 not PII ) |
message String | A message indicating what happened with the request. (🏢 not PII ) |
cellphone String | The country code and last two digits of phone number used to send the message, with the rest obfuscated. (🏢 not PII ) |
ignored Boolean | True if we detected an Authy or an SDK enabled app installed and we upgraded the OTP delivery channel from 'Voice' to Push Notification. Authy or SDK users are redirected directly to the requested token. (🏢 not PII ) |
device String | The type of the last device used by the user. This is only returned when we upgraded delivery from a voice call. (🏢 not PII ) |
1# Download the SDK from https://github.com/twilio/authy-python2from authy.api import AuthyApiClient34# Your API key from twilio.com/console/authy/applications5# DANGER! This is insecure. See https://twil.io/secure6authy_api = AuthyApiClient('api_key')78call = authy_api.users.request_call(authy_id)910if call.ok():11print call.content
Output
1{2"success":true,3"message":"Call started...",4"cellphone":"+1-XXX-XXX-XX02"5}
If the user has the Authy App, by default, the API will not call the user. See above for more details. The API response will look like this:
1{2"message": "Call ignored. User is using App Tokens and this call is not necessary. Pass force=true if you still want to call users that are using the App.",3"cellphone": "+1-XXX-XXX-XX02",4"device": "android",5"ignored": true,6"success": true7}
Like SMS, you can pass force=true as a parameter to this API. This will force the phone call to start even if the user is using the Authy app.
To verify a one-time password pass in the user provided token and the user authy_id. Twilio will use HTTP status codes for the response.
GET https://api.authy.com/protected/{FORMAT}/verify/{TOKEN}/{AUTHY_ID}
| Name | Description |
|---|---|
FORMAT String | The format to expect back from the REST API call. json, or xml. |
TOKEN Integer | The token you are verifying. |
AUTHY_ID String | The Authy ID of the user validating the TOTP. Create an Authy ID by registering a user. |
| Name | Description |
|---|---|
200 | Valid token (see note below)* |
401 | Invalid token. If you wish to verify the token anyway, pass force=true. See the force verification section below for an example. |
Note: Until you successfully verify a token for a new user, this call will return 200.
| Name | Description |
|---|---|
token String | Either "is valid" or "is invalid" (🏢 not PII ) |
success String | "true" if the code was valid. Note: This field is a String and not a Boolean. (🏢 not PII ) |
device Object | An object including some details about the device used to get or generate the token. The fields included in the device object are: city, region, country, ip, registration_city, registration_region, registration_country, registration_ip, registration_date, os_type, last_account_recovery_at and id. (📇 PII ) |
When the TOTP token is generated in the Authy app or in the SDK, additional device information and registration data are provided in the response.
1# Download the SDK from https://github.com/twilio/authy-python2from authy.api import AuthyApiClient34# Your API key from twilio.com/console/authy/applications5# DANGER! This is insecure. See https://twil.io/secure6authy_api = AuthyApiClient('api_key')78verification = authy_api.tokens.verify(authy_id, token='1234567')9print(verification.ok())
Output
1{2"message": "Token is valid.",3"token": "is valid",4"success": "true",5"device": {6"city": "San Francisco",7"country": "United States",8"ip": "97.20.126.156",9"region": "California",10"registration_city": "San Francisco",11"registration_country": "United States",12"registration_device_id": 456456,13"registration_ip": "97.34.234.11",14"registration_method": "push",15"registration_region": "California",16"os_type": "android",17"last_account_recovery_at": null,18"id": 83372911,19"registration_date": 149099693120}21}
The same API is used to verify tokens from TOTP, sms, and voice channels. However when the OTP token is delivered via SMS or voice call, no additional device details are provided and the response will look like:
1{2"message": "Token is valid.",3"token": "is valid",4"success": "true",5"device": {6"id": null,7"os_type": "sms",8"registration_date": 1490996931,9"registration_method": null,10"registration_country": null,11"registration_region": null,12"registration_city": null,13"country": null,14"region": null,15"city": null,16"ip": null,17"last_account_recovery_at": null,18"last_sync_date": null19}20}
Use force=true to force verification of a one-time password from a new user.
1curl -i "https://api.authy.com/protected/json/verify/{TOKEN}/{AUTHY_ID}" \2-H "X-Authy-API-Key: d57d919d11e6b221c9bf6f7c882028f9"
1{2"token":"Not checked. User has not yet finished the registration process. Pass force=true to this API to check regardless (more secure)."3}
1{2"errors": {3"token":"is invalid"4}5}
When using custom actions to send SMS you have to pass action= to validate the one-time password.
For more information see Custom Actions.
1{2"token": "is valid"3}
A verification attempt with an invalid token will return a 401 Unauthorized with the following Response body:
1{2"message": "Token is invalid",3"token": "is invalid",4"success": false,5"errors": {6"message": "Token is invalid"7},8"error_code": "60020"9}
1# Download the SDK from https://github.com/twilio/authy-python2from authy.api import AuthyApiClient34# Your API key from twilio.com/console/authy/applications5# DANGER! This is insecure. See https://twil.io/secure6authy_api = AuthyApiClient('api_key')78# Available in version 2.2.4+9response = api.users.generate_qr(authy_id, size=200, label="My Example App")1011print(response.content['qr_code'])
Output
1{2"label": "AppName(myuser@example.com)",3"Issuer": "AppName",4"qr_code": "https://[qr_code]",5"success": true6}
When you enroll a user, they will automatically be able to generate Soft Token TOTP codes in the Authy App if they register for Authy with the same phone number that you used to enroll them. You do not need to do anything additional to take advantage of the Authy app. You can disable this behavior with the 'Sync tokens in Authy app' setting in the Authy settings in the Twilio Console.
To validate these One-Time Passwords, see Verify a One-Time Password below.
To support other Authenticator apps, like Google Authenticator, display a QR code to your users that contain a compatible OTP secret. The API will return a link to a valid QR code.
To customize the QR label and give the final user context about the token like account name or email, you can include the label param in the QR generation endpoint. That way many Authenticator apps will automatically render the label in the token list.
To enable, browse to your Authy application in the Twilio Console. Click on your App's Settings and scroll to the bottom.
Note: Each QR code request will generate a unique TOTP seed. You can only have a single active QR code per user per protected site. Requesting an additional QR code for a user will invalidate the previous secret and generate a new QR code.
When providing a QR code to a user, be sure to have them validate the code before applying 2FA protection to their account.
Info
QR codes expire in 24 hours.
POST https://api.authy.com/protected/{FORMAT}/users/{AUTHY_ID}/secret
| Name | Description |
|---|---|
FORMAT String | The format to expect back from the REST API call. json or xml. |
AUTHY_ID Integer | The Authy ID of the user to send an SMS TOTP. Create an Authy ID by registering a user. |
| Name | Description |
|---|---|
qr_size Integer (optional) | Dimension of the QR code that will be returned. Square, so only one number required. Default value is 256. Max value is 320. (🏢 not PII ) |
label String (optional) | A custom label for the QR code, this field will be shown by the Authenticator app, it gives context to the user, like the account email. Default value is the application name. (📇 PII ) |