Preventing Fraud in Verify
One of the challenges of operating globally is the increased exposure to fraud. There are two types of attacks we commonly see in phone verification or two-factor authentication (2FA) flows.
- SMS pumping
- International Revenue Sharing Fraud (IRSF) also known as "Toll Fraud"
Both attacks cause inflated traffic to your app with the intent to make money and not to steal information. While the specific ways attackers monetize these types of fraud is different, the strategies you can implement to reduce fraud are similar.
Danger
Customer participation is essential to successfully defend against fraud. Our Verify product includes comprehensive built-in fraud detection and mitigation mechanisms. However, no provider-side solution can guarantee 100% effectiveness against sophisticated attackers.
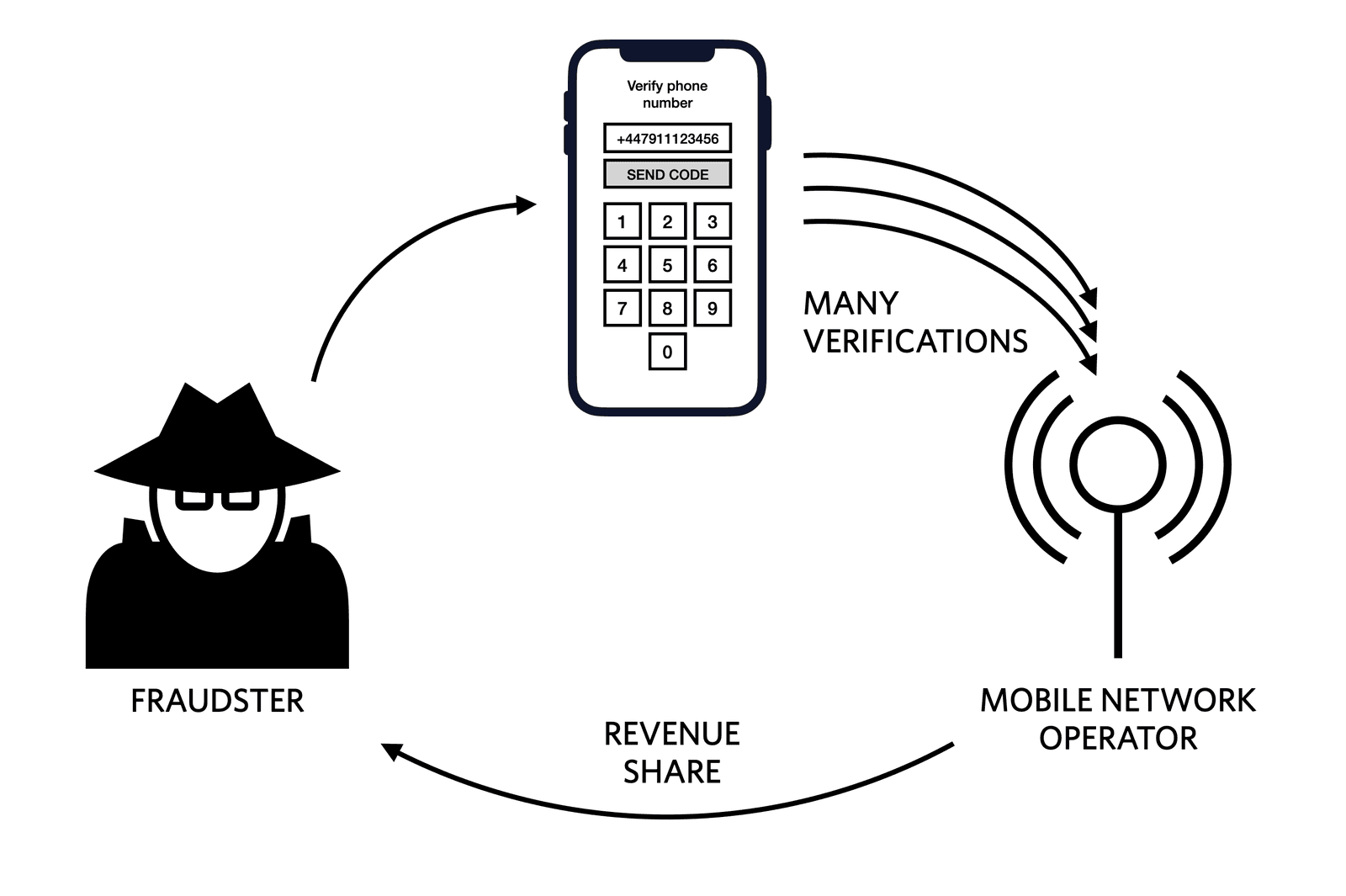
SMS pumping fraud happens when fraudsters take advantage of a phone number input field to receive a one-time passcode, an app download link, or anything else via SMS. The messages are sent to a range of numbers controlled by a specific mobile network operator (MNO) and the fraudsters get a share of the generated revenue.
See the SMS Pumping Fraud glossary entry for more information.
Toll fraud, also known as International Revenue Sharing Fraud (IRSF), happens when an application is exploited to generate a high volume of voice calls to the fraudster's own international premium rate numbers. The victim of the toll fraud bears the entire financial responsibility for each minute of the call.
See the Toll Fraud glossary entry for more information.
Twilio recommends enabling the SMS fraud guard on your account. When enabled, this feature will block the transmission of suspicious and likely fraudulent SMS messages preventing unnecessary charges to your account.
If you don't plan to allow any calls, you can disable that channel by selecting the Service on the Console, selecting the Voice tab, and disabling the channel.
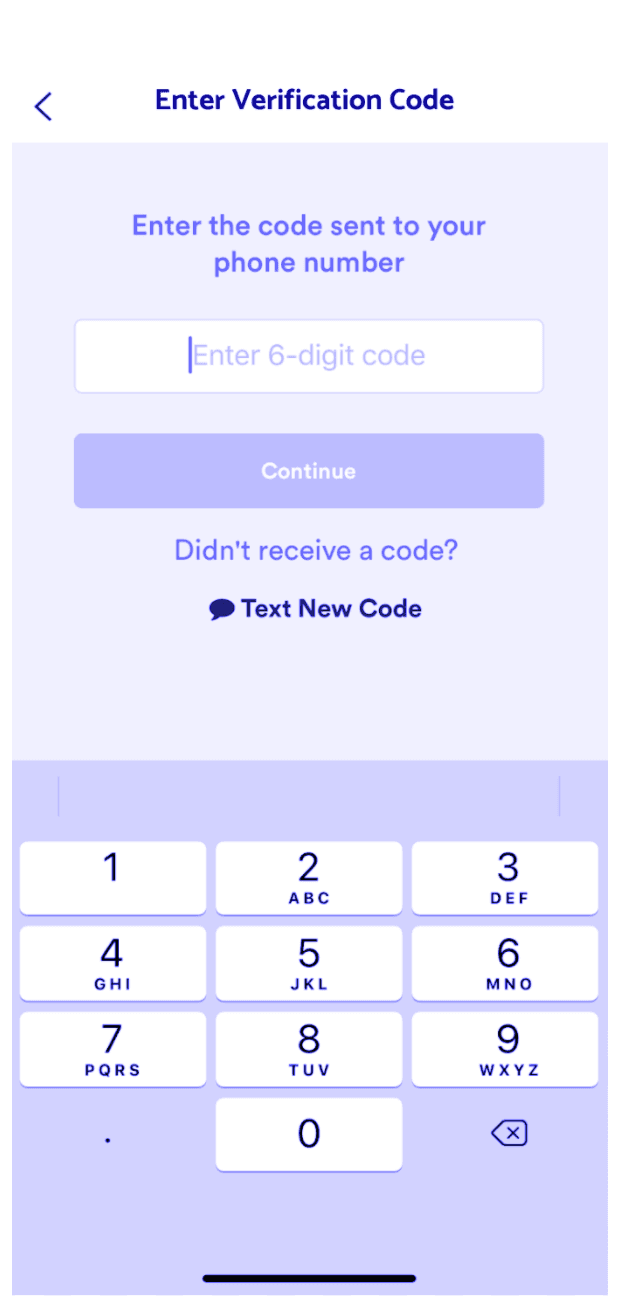
Similar to rate limits, implementing exponential delays between requests to the same phone number is one way to prevent rapid sending. Learn more about our recommendations for retry logic for SMS 2FA in this blog post.
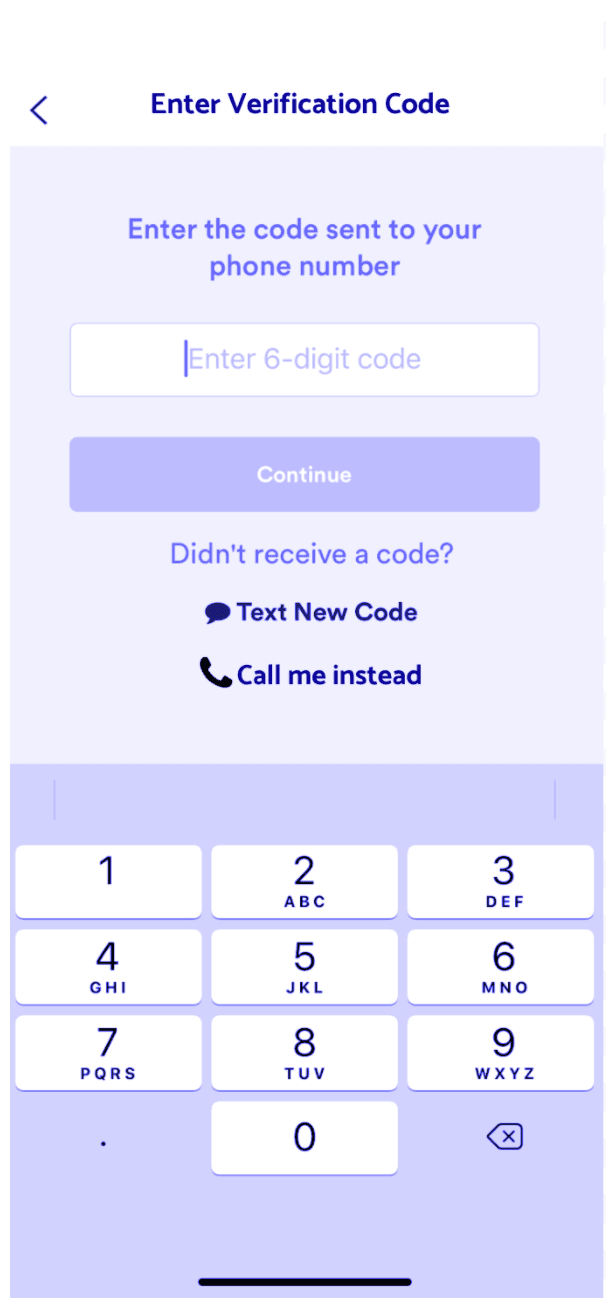
| Good Example - "Call me instead" option is not visible until 3 time-delayed SMS attempts. | Bad Example - "Call me instead" option is visible at any time and can be repeatedly submitted. |
|---|---|
 |  |
Add Service Rate Limits for your Verification Service.
Make sure your app will not send more than 1 message per X seconds to the same mobile number range or prefix. Implement rate limits by user, IP, or device identifier. You can use a CDN like Cloudflare or implement modules in your web server like Nginx and Apache for basic rate limiting.
Rate limits may not prevent fraud but can slow the attackers down enough that they decide it's not worth it to go after your app.
Libraries like botd or CAPTCHAs can help detect and deter bot traffic. Small changes to your user experience like ensuring that your users confirm their email address before enrolling in 2FA introduce a small amount of friction for legitimate users but can deter automated scripts and bots.
Learn more about best practices for phone verification and 2FA.
Use Carrier Lookup to get the line type of a number then only send SMS to mobile numbers. You can also use this API request to determine the carrier and block carriers that may be (knowingly or not) causing inflated traffic. Learn more about how to build a carrier block list with Lookup in this blog post.
Create internal monitors for conversion rate of verifications (i.e number of OTPs validated by end users / number of OTPs sent to end users). If you notice this rate start to drop, especially in an unexpected country, trigger an alert for manual review.
You can also configure a usage trigger on your Twilio account to alert you when your usage goes above a certain threshold.
Analyze IP location, IP owner (ISP/proxy/TOR/cloud provider, etc), and IP against the bad reputation list. Block TOR/Cloud Providers/proxies/bad IPs.
While there are legitimate use cases for VPNs, attackers will likely use one to bypass simple I.P. address blocking and this is a signal that something might be awry. There are a lot of solutions for VPN detection out there to choose from.
Review your Verify Geographic Permissions and disable all countries that you do not plan to send messages to.
You can also build a programmatic allow list or block list based on the country codes of the phone number with our free Lookup formatting API.
If you have data on the number of verifications you'd expect per day in a given country, you can set rate limits on groups of countries, allowing relaxed rate limits in countries where you expect legitimate users, and more restricted rate limits in all other countries.
Email fraud@twilio.com if you are facing messaging abuse. Please include the following details in your message:
1Account SID:2Product Type:3Date/time Range:4To/Recipient Country:5Workspace SID:6Description of Activity:
Here are some more resources for account security that you might enjoy: