How to protect your account from toll fraud with Voice Dialing Geo Permissions
Time to read:
This post is part of Twilio’s archive and may contain outdated information. We’re always building something new, so be sure to check out our latest posts for the most up-to-date insights.

Did you know that International Revenue Sharing Fraud (IRSF), also known as toll fraud, leads to $10 billion dollars in annual revenue losses globally and has grown six-fold in the past five years? Care for a horror story? Read about this seven person architecture firm in Georgia that came to work on a Monday to find a $166,000 bill from their local telecom provider.
Teams of criminals are continuously looking for ways to exploit your apps by placing calls to their international premium rate numbers – a virtual wire-transfer from your company’s bank account to theirs.
Now with a few clicks on the Twilio Console, you can take one big step to further protect your application from being the next victim of toll fraud.
There’s no silver bullet with toll fraud. Before we dive into Twilio’s dynamic solution to prevent toll fraud, it’s important to understand that there is no single solution to completely prevent toll fraud. The creation and reselling of number ranges is very dynamic – every week there are more than 10,000 new IRSF ranges being advertised. Combating toll fraud requires a multi-pronged approach. It is important to continuously monitor your account and sub-account usage for any unwanted abuse. Usage triggers let you suspend the accounts exceeding daily limits.
To learn more about toll fraud read Twilio’s guide here.
How Twilio classifies destinations according to risk
toll fraud attacks terminate calls across 200+ countries, across all number types, wide price ranges, and are carried out by a well-coordinated team of criminals distributed around the globe. In Telecom, the caller, the victim of the toll fraud, bears the entire financial responsibility for each minute of a call, as mandated by the FCC. In order to help protect Twilio customers’, Twilio has classified number ranges in each country by risk of toll fraud.
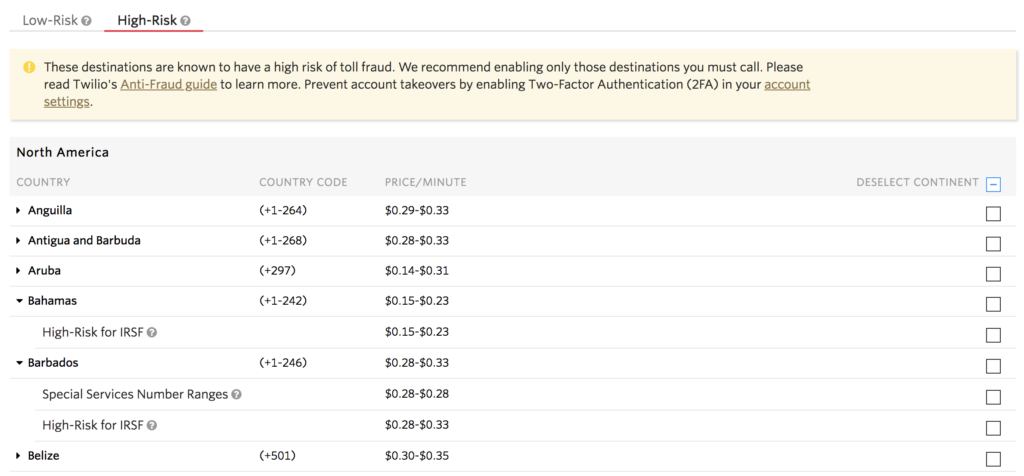
All Countries have a low-risk permission group
By default, a number range falls into the low-risk category, unless there is a reason to believe the range is risky so by enabling the low-risk range most businesses can call all their customers.
Countries also have one or two high-risk permission groups
- Special Services number ranges include premium, shared-cost, and special services number types. These number ranges change infrequently and can be viewed in the Console.
- High risk for IRSF number ranges include narrow ranges from 3rd party anti-fraud databases and from analyzing millions of calls on the Twilio Super Network. Since these numbers can be bought and sold nearly instantly, Twilio regularly updates the list. These ranges are not disclosed to further protect your account.
How to reduce risk on your account
Navigate to the Geo Permissions High-Risk tab and de-select every country with a high-risk checkbox enabled. To quickly disable all countries, use the deselect continent checkbox. Click Save.
Careful not to disable low-risk tab because you will block most of your outbound calls.
How do I know if my calls are being blocked by Geo Permissions?
Inspect your blocked calls so you ensure your legitimate customers can call the destinations they need to call. You can easily do this by navigating to the debugger and search for the warnings 21215, 32205, 13227, which correspond to calls blocked that were initiated by – SIP Trunking, , and the REST API. Calls blocked by Geo Permissions could indicate that Fraudsters are trying to abuse your application so you should take additional steps to protect your account.
What happened to my old Geo Permissions?
Twilio has migrated your permissions on your Project(s) and sub-accounts. All destinations that you were previously able to call, are now enabled in the new Console page. This means that if you had enabled calling to every global destination in the old Geo Permission page, you will have high-risk enabled for every country in the new Geo Permission page.
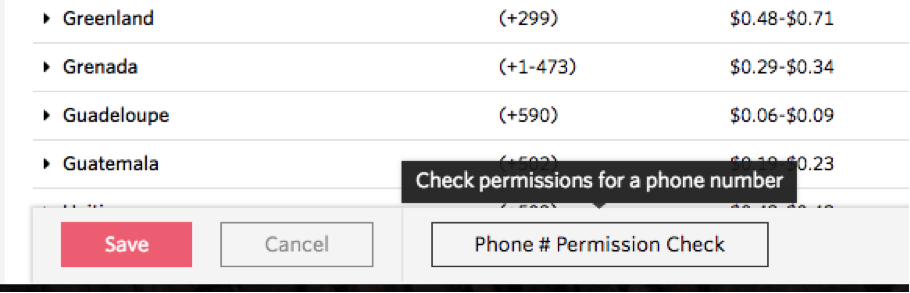
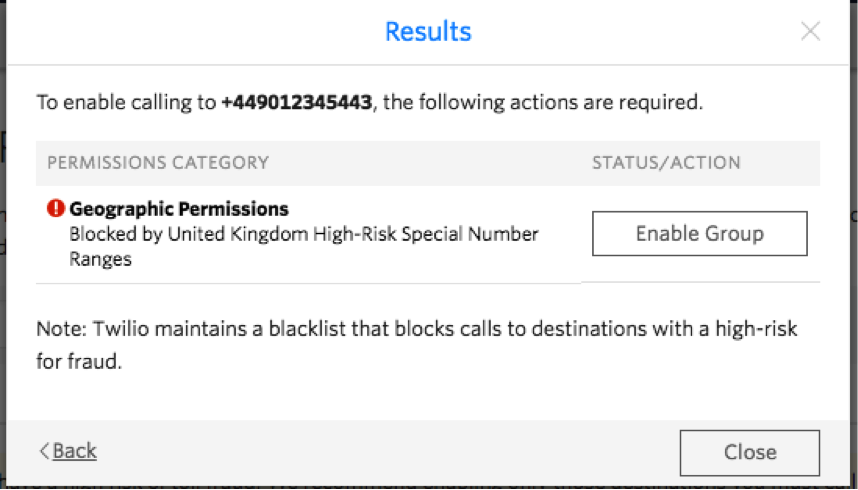
Which permission group to enable to call a telephone number?
You can view the prefixes in the High-Risk Special Services prefix group. Twilio does not disclose the prefixes in the High-Risk – IRSF permission group. You can use the Phone Number Permission check in order to see which group you must enable to call a particular phone number.
How do Fraudsters carry out a toll fraud attack?
There are a few steps involved in toll fraud attacks
- Fraudsters gain access to a PBX or app that lets them place outbound calls.
- Fraudsters place short duration calls to test numbers, provided by the international premium rate resellers, to find holes not blocked by the chain of telecom carriers.
- Once a test number can be reached, Fraudsters then purchase an International Premium rate number from the reseller.
- Within 30 minutes, the attacker will create dozens of concurrent calls to the number(s) they just purchased.
- The terminating carrier pays the fraudster according to a revenue-sharing agreement.
- The victim of the attack is required by law to cover the telecom charges carried out on their account
You can learn more, explore Twilio’s user documentation, or read more in-depth with Twilio’s Anti-Fraud Developer Guide.
Related Posts
Related Resources
Twilio Docs
From APIs to SDKs to sample apps
API reference documentation, SDKs, helper libraries, quickstarts, and tutorials for your language and platform.
Resource Center
The latest ebooks, industry reports, and webinars
Learn from customer engagement experts to improve your own communication.
Ahoy
Twilio's developer community hub
Best practices, code samples, and inspiration to build communications and digital engagement experiences.