Verify Python Flask Quickstart
With just a few lines of code, your Python application can verify phone numbers and add an additional layer of security with Twilio Verify.
This Python Verify Quickstart will teach you how to do this using our Verify REST API, the Twilio Python SDK, and Python's Flask microframework to ease development.
In this Quickstart, you will learn how to:
- Sign up for Twilio
- Set up your development environment
- Send your first SMS, voice or WhatsApp phone verification
- Check verification codes
Info
Short on time? Spin up a low-code, fully editable verification demo in less than 2 minutes using Twilio's Code Exchange and Quick Deploy here.
If you already have a Twilio account, you're all set here! Feel free to jump to the next step.
Before you can send a phone verification from Python, you'll need to sign up for a Twilio account or sign into your existing account.
You can sign up for a free Twilio trial account here.
- When you sign up, you'll be asked to verify your personal phone number. This helps Twilio verify your identity and also allows you to send test verification messages to your phone from your Twilio account while in trial mode. This phone verification step is exactly what you'll learn how to build in this tutorial!
- Once you verify your number, you'll be asked for your Twilio introduction preference. For the sake of this tutorial, you can select "I just need my Account SID and Auth Token".
- You'll arrive at your project dashboard in the Twilio Console. This is where you'll be able to access your Account SID and authentication token, create a verification service, and more.
If you've sent SMS with Twilio in the past, you might remember needing to buy a phone number. With Twilio Verify, we take care of that for you! The Verify API selects the best routes for quickly and reliably delivering verification codes globally.
Verify uses services for configuration. To send a Verify API request you will need both your Twilio Credentials and a Service SID. You can create and update a Service in two ways:
- In the Verify Console
- With the Verify API
Create a new Service using one of these methods. Services can be used to edit the name (which shows up in the message template), set the code length (4-10 characters), enable settings like the "do not share warning" and more.
Now that you have a Twilio account and a Verify Service, you can start writing some code! To make things even easier, we'll next install Twilio's official helper for Python applications.
If you've gone through one of our other Python Quickstarts already and have Python and the Twilio Python SDK installed, you can skip this step and get straight to sending your first verification.
To start a phone verification, you'll need to have Python and the Twilio Python SDK installed.
If you're using a Mac or Linux machine, you probably already have Python installed. You can check this by opening up a terminal and running the following command:
python --version
You should see something like:
1$ python --version2Python 3.4 # Python 2.7+ is okay too
Windows users can follow this excellent tutorial for installing Python on Windows, or follow the instructions from Python's documentation.
Twilio's Python SDK supports both Python 2 and Python 3. You can use either version for this quickstart, but we recommend using Python 3 for future projects with Twilio unless there are specific libraries your project needs which are only compatible with Python 2.
1# Download the helper library from https://www.twilio.com/docs/python/install2import os3from twilio.rest import Client45# Find your Account SID and Auth Token at twilio.com/console6# and set the environment variables. See http://twil.io/secure7account_sid = os.environ["TWILIO_ACCOUNT_SID"]8auth_token = os.environ["TWILIO_AUTH_TOKEN"]9client = Client(account_sid, auth_token)1011verification = client.verify.v2.services(12"VAaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa"13).verifications.create(channel="sms", to="+15017122661")1415print(verification.status)
Response
1{2"sid": "VEaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa",3"service_sid": "VAaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa",4"account_sid": "ACaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa",5"to": "+15017122661",6"channel": "sms",7"status": "pending",8"valid": false,9"date_created": "2015-07-30T20:00:00Z",10"date_updated": "2015-07-30T20:00:00Z",11"lookup": {},12"amount": null,13"payee": null,14"send_code_attempts": [15{16"time": "2015-07-30T20:00:00Z",17"channel": "SMS",18"attempt_sid": "VLaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa"19}20],21"sna": null,22"url": "https://verify.twilio.com/v2/Services/VAaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa/Verifications/VEaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa"23}
1# Download the helper library from https://www.twilio.com/docs/python/install2import os3from twilio.rest import Client45# Find your Account SID and Auth Token at twilio.com/console6# and set the environment variables. See http://twil.io/secure7account_sid = os.environ["TWILIO_ACCOUNT_SID"]8auth_token = os.environ["TWILIO_AUTH_TOKEN"]9client = Client(account_sid, auth_token)1011verification_check = client.verify.v2.services(12"VAaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa"13).verification_checks.create(to="+15017122661", code="123456")1415print(verification_check.status)
Response
1{2"sid": "VEaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa",3"service_sid": "VAaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa",4"account_sid": "ACaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa",5"to": "+15017122661",6"channel": "sms",7"status": "approved",8"valid": true,9"amount": null,10"payee": null,11"sna_attempts_error_codes": [],12"date_created": "2015-07-30T20:00:00Z",13"date_updated": "2015-07-30T20:00:00Z"14}
Start by cloning our Flask repository.
git clone git@github.com:TwilioDevEd/verify-v2-quickstart-python.git
If you don't have git installed or prefer to download the source code you can grab a zip file of the project here.
If you're not familiar with Python virtual environments, follow our tutorial for setting up your local Python environment. Navigate into the project folder and create your virtual environment.
1cd verify-v2-quickstart-python23virtualenv venv4source venv/bin/activate56pip install -r requirements.txt
Copy .env.example to .env. This is where we'll store sensitive data in environment variables.
cp .env.example .env
Run the application
1export FLASK_APP=verify2export FLASK_ENV=development3flask init-db4flask run
Or on Windows cmd:
1set FLASK_APP=verify2set FLASK_ENV=development3flask init-db4flask run
If your credentials are set up correctly you'll soon get a message that the app is up!
Navigate to http://localhost:5000/auth/register. You should see a registration form that looks like this:
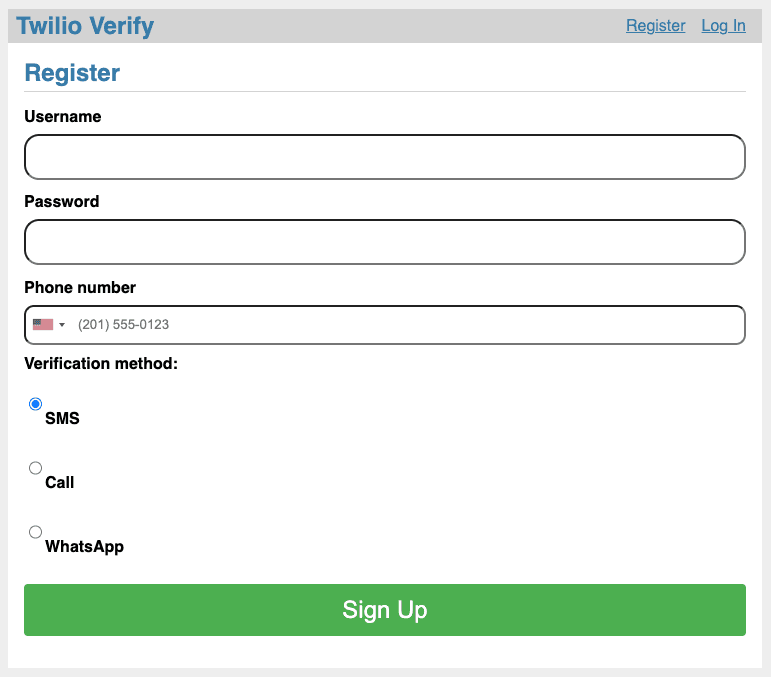
Enter your phone number and choose which channel to request verification over. Finally hit the green Sign Up button and wait. You'll either receive an SMS, phone call, or WhatsApp message with the verification token. If you requested a phone call, as an additional security feature you may need to interact to proceed (the call will tell you to enter a number on the phone keypad).
Enter the token into the Verification entry form and click 'Verify':
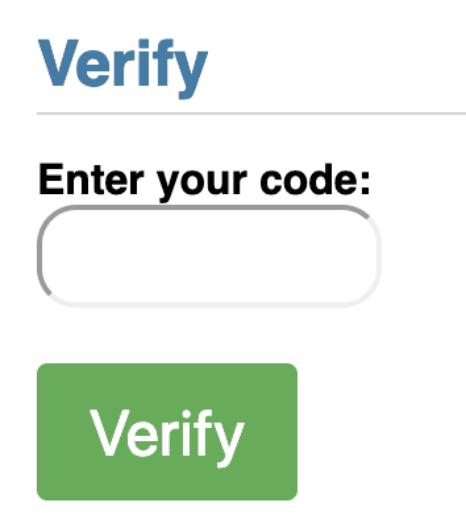
And with that, your demo app is protected with Twilio's Phone Verification!
Your demo app is now keeping fraudulent users from registering with your business and polluting your database. Next, check out all of the variables and options available to you in the Verify API Reference.
After that, check out adding additional verification channels supported by the Verify API like:
Info
Lastly, to protect your service against fraud, view our guidance on Preventing Toll Fraud when using Verify.