-
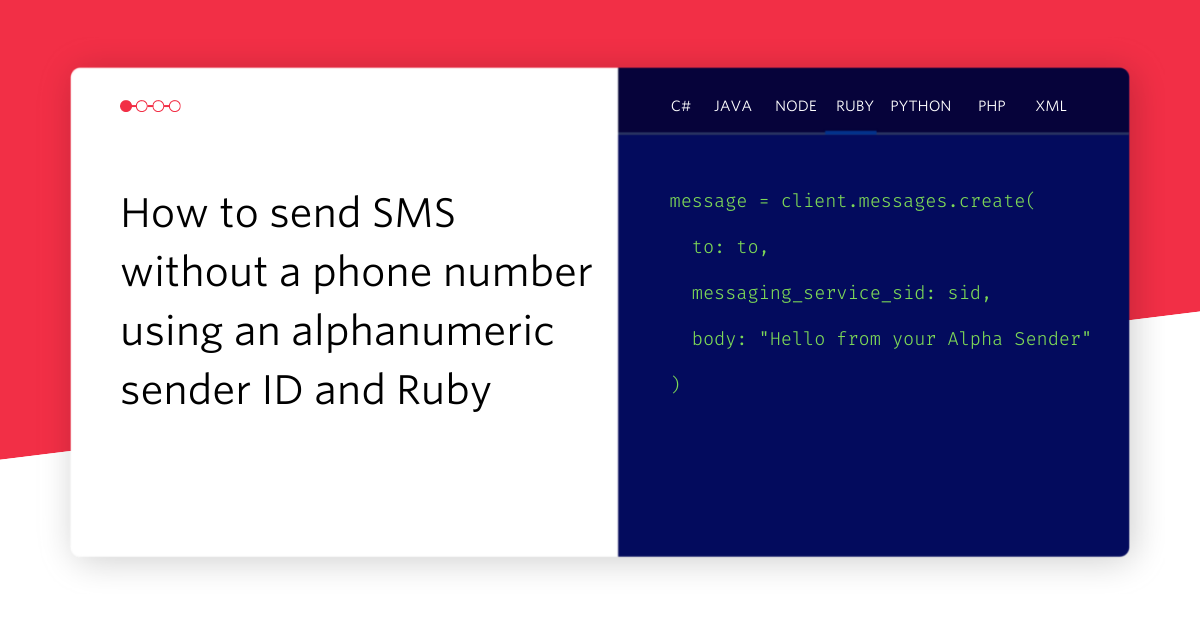 How to send SMS Without a Phone Number using Alpha Sender and RubyPhil Nash
How to send SMS Without a Phone Number using Alpha Sender and RubyPhil Nash -
 Send Scheduled SMS with Ruby and TwilioMiguel Grinberg
Send Scheduled SMS with Ruby and TwilioMiguel Grinberg -
 How to Send an SMS in 30 Seconds with RubyMatthew Setter
How to Send an SMS in 30 Seconds with RubyMatthew Setter -
 Build a Video Chat Application with Ruby, JavaScript, and Twilio Programmable VideoMia Adjei
Build a Video Chat Application with Ruby, JavaScript, and Twilio Programmable VideoMia Adjei -
 Send a WhatsApp Message in 30 Seconds with RubyValeriane Venance
Send a WhatsApp Message in 30 Seconds with RubyValeriane Venance -
 Send vCards with Ruby and TwilioValeriane Venance
Send vCards with Ruby and TwilioValeriane Venance -
 5 ways to make HTTP requests in RubyValeriane Venance
5 ways to make HTTP requests in RubyValeriane Venance -
 Building Voicemail with Twilio and RubyValeriane Venance
Building Voicemail with Twilio and RubyValeriane Venance -
 Coding a Rails lookup SMS app for my grandparentsValeriane Venance
Coding a Rails lookup SMS app for my grandparentsValeriane Venance