How to Protect Your Android Phone From the Stagefright Bug
Time to read:
This post is part of Twilio’s archive and may contain outdated information. We’re always building something new, so be sure to check out our latest posts for the most up-to-date insights.

Earlier this morning, a vulnerability was disclosed for Android phones performing a remote code execution over MMS. Dubbed “Stagefright“, the vulnerability exploits SMS/MMS clients by sending a malformed media file to the user which is automatically downloaded by the default client.
If you’re using Google Hangouts as your default SMS client, here’s how to protect your device from Stagefright by disabling automatic downloading of media files sent via MMS:

Here’s how to protect your phone from the Stagefright bug if you’re using Google Messenger (the default SMS client for Android 5.0+):

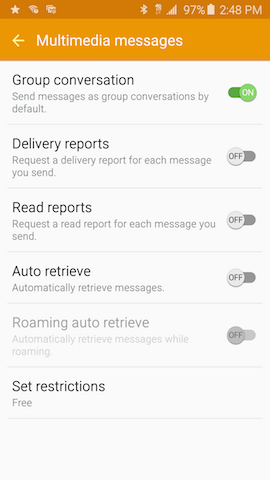
The above screenshots were taken on a Nexus 5, but the steps are the same on any Android device using Hangouts or Messenger. To disable Auto Retrieve MMS in the default SMS client on the Samsung Galaxy S6, go to:
- Messages app
- More
- Settings
- More settings
- Multimedia messages
- Auto retrieve
The final Multimedia messages setting should look like this:
More on the Stagefright Hack
From NPR’s Major Flaw In Android Phones Would Let Hackers In With Just A Text:
Here’s how the attack would work: The bad guy creates a short video, hides the malware inside it and texts it to your number. As soon as it’s received by the phone, Drake says, “it does its initial processing, which triggers the vulnerability…”
Once the attackers get in, Drake says, they’d be able do anything — copy data, delete it, take over your microphone and camera to monitor your every word and move. “It’s really up to their imagination what they do once they get in,” he says.
Disabling Auto Retrieve MMS will partially mitigate this vulnerability ahead of the official patch release. All MMS media files will require a click in order to be viewed, but disabling this feature will prevent an attack from automatically executing on your phone. Turning off this feature does not fix the exploit entirely. So long as the bug exists, your Android device remains vulnerable and can be hacked if a malformed media file is downloaded by clicking on it. This vulnerability will not be completely fixed until a patch is released for your device, but this intermediate step can help mitigate the threat in the meantime.
To learn more about the exploit, check out:
- The ‘Stagefright’ exploit: What you need to know (Android Central)
- Stagefright: It Only Takes One Text To Hack 950 Million Android Phones (Forbes)
- ‘Stagefright’ Android bug is the ‘worst ever discovered’ (Wired)
This guide is for the versions of Google Hangouts and Google Messenger that ship with the latest version of Android Lollipop (5.1.1). If the steps are different for your version or Android, or if your phone ships with a different default SMS client, please reach out to me at gb@twilio.com and we’ll update this post.
Thank you to Ricky, Rob, Christopher, Kyle, Sam and Jarod for their contributions to this post, to jimrandomh on HN for pointing us down this mitigation path, and to Greg Bulmash for providing the Galaxy instructions.
Related Posts
Related Resources
Twilio Docs
From APIs to SDKs to sample apps
API reference documentation, SDKs, helper libraries, quickstarts, and tutorials for your language and platform.
Resource Center
The latest ebooks, industry reports, and webinars
Learn from customer engagement experts to improve your own communication.
Ahoy
Twilio's developer community hub
Best practices, code samples, and inspiration to build communications and digital engagement experiences.