How is Push Authentication different from Push Notifications?
Time to read:
This post is part of Twilio’s archive and may contain outdated information. We’re always building something new, so be sure to check out our latest posts for the most up-to-date insights.
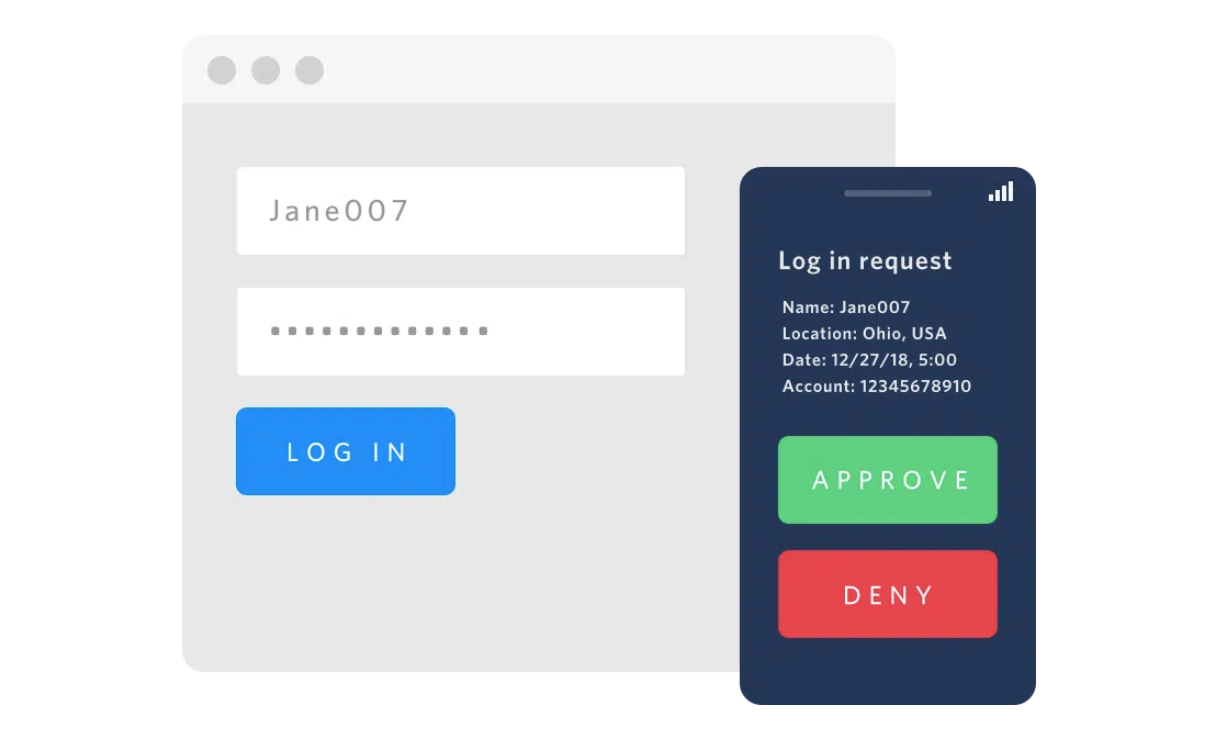
Push authentication is one of the most secure and user friendly forms of authentication. Instead of typing in a one-time passcode, a user taps "approve" or "deny" (or "yes" or "no") on an authorized mobile device. Twilio Verify offers an SDK to embed push authentication directly into your mobile application, especially useful if you have a large mobile user base.
Some customers already have a push notification system built and consider using that for delivering authentication. This blog post will outline some of the key differences between push authentication and push notifications and why we recommend an authentication-specific solution.
Why you should use push authentication instead of just push notifications
Push authentication is more secure than push notifications
Push authentication relies on public-key infrastructure. Our SDK turns each device into a secure key, making push authentication phishing resistant. A push notification alone doesn't have the same assurance.
Push authentication still works with disabled/blocked notifications
If a user blocks notifications, a Verify Push authentication challenge will still show up when the user opens the app.
In addition, standard push services are not designed for time critical circumstances. Verify Push doesn't rely on the mobile push service alone: the authentication challenge is stored in the backend and can be retrieved immediately whenever the app is opened by the user.
Push authentication allows for silent verification
Silent verification, where the app does background authentication using the stored private key, won't work with a push notification. The beauty of silent verification is that it doesn't require any notifications, instead you fetch the authentication challenge in the background (with webhooks or polling) so you'll need to build that separately from your notification service.
Apple discourages using notifications for sensitive information
According to app store review guidelines, "Push Notifications must not be required for the app to function, and should not be used to send sensitive personal or confidential information." Unlike a notification only solution, a Verify Push challenge can include additional sensitive information like email address or login location in the in-app challenge screen. Depending on your implementation, including sensitive information in the notification may cause issues getting your app approved in the App Store.
Note: push authentication challenges are not encrypted so we recommend additional protections like certificate pinning to prevent a man-in-the-middle attack.
Verify Push complies with authentication regulation like PSD2
Payment Services Directive 2 (PSD2) is European regulation that requires Strong Customer Authentication on electronic payment over €30. This means that businesses need to send additional context for transactions like the amount and payee. Verify Push is PSD2 compliant and will make sure your business stays compliant with any new regulations that may be introduced.
Getting started with Verify Push
If you still have questions about whether Verify Push is the right solution for you, please get in touch. You can learn more with our Verify Push general overview, technical overview, and best practices.
If you're ready to start building, check out the following quickstarts for your platform[s]:
I can't wait to see what you build and secure!
Related Posts
Related Resources
Twilio Docs
From APIs to SDKs to sample apps
API reference documentation, SDKs, helper libraries, quickstarts, and tutorials for your language and platform.
Resource Center
The latest ebooks, industry reports, and webinars
Learn from customer engagement experts to improve your own communication.
Ahoy
Twilio's developer community hub
Best practices, code samples, and inspiration to build communications and digital engagement experiences.

