-
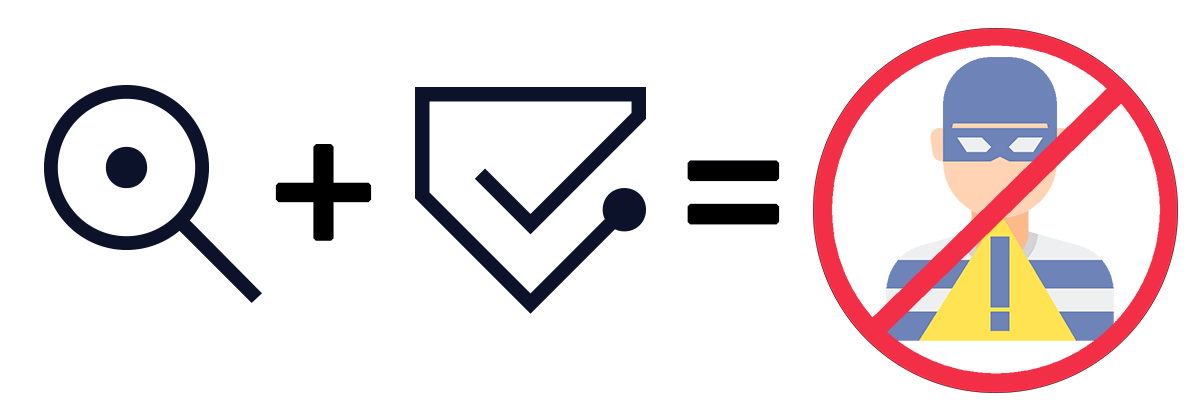 Fraud Prevention with Twilio User Authentication & IdentityJosh Staples
Fraud Prevention with Twilio User Authentication & IdentityJosh Staples -
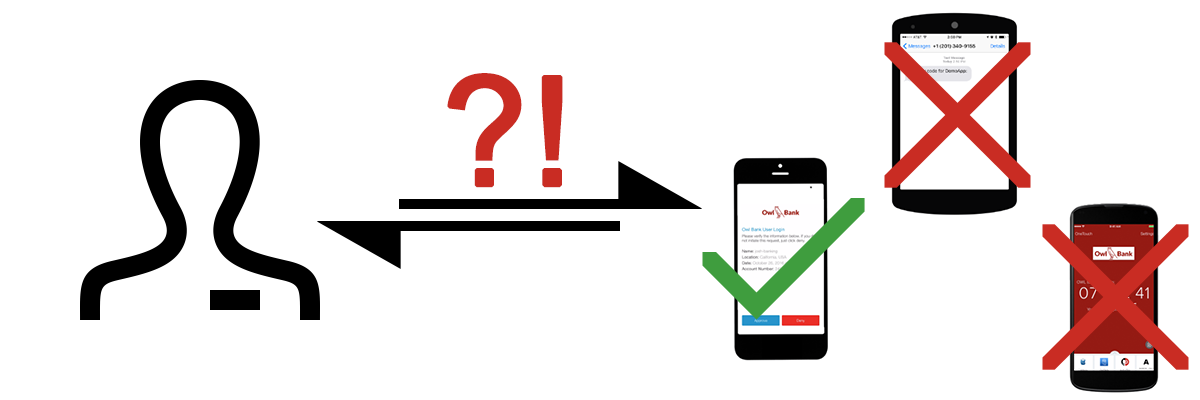 Elevated Authentication with AuthyJosh Staples
Elevated Authentication with AuthyJosh Staples -
 Secure FreeRADIUS VPN Users With Twilio 2FAJosh Staples
Secure FreeRADIUS VPN Users With Twilio 2FAJosh Staples -
 Easily Manage Team Access To The Twilio ConsoleJosh Staples
Easily Manage Team Access To The Twilio ConsoleJosh Staples -
 Onboarding Authy UsersJosh Staples
Onboarding Authy UsersJosh Staples -
 Quick and Easy 2FA: Adding Authy to a NodeJS AppJosh Staples
Quick and Easy 2FA: Adding Authy to a NodeJS AppJosh Staples