Smishing: SMS Phishing Explained
Time to read:

With the rise of attacks using familiar everyday tech as vectors, it's important to discuss the difference between a legitimate, bulk SMS and a well-crafted, malicious SMS designed to access your data or use your device for more nefarious actions.
In this article, we provide an overview of an increasingly common cyberattack that relies on the common usage of SMS as a platform, SMS phishing, and how it differs from bulk SMS. We'll walk through examples of SMS phishing, highlight what you should watch out for, and help you recognize legitimate SMS communications.
What is phishing?
Phishing is a cyberattack that disguises common communication platforms, such as email or messaging services, as a weapon. The goal of this attack is to trick the recipient into believing that the message is urgent and something that they want or need.
Typically, these attacks can include:
- A request from their bank to log in and change a password or provide contact information.
- A message promising a gift card.
- An email claiming to be from a high-level executive.
- An email from IT designed to get the recipient to download or install an application on their computer.
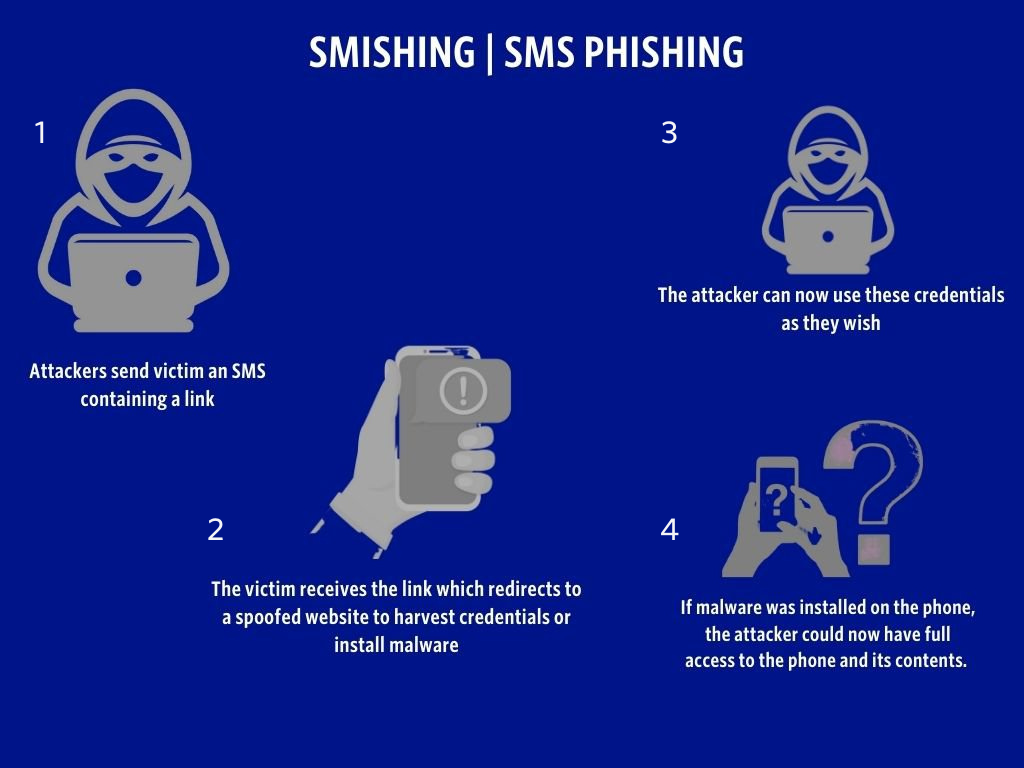
In a web-based attack, the attacker redirects the end user to a counterfeit website it owns. Then the attacker scams the victim into providing bank details, paying a fee or charge, or entering other credentials as part of a larger attack.
If the goal is to get the user to install an application, once they click the link, the malicious payload is on the device. The device is then considered to be compromised, which provides a foothold for a larger attack (e.g., on a company’s network).
What is smishing?
With the wide adoption of SMS, it wasn’t long before smishing, or SMS phishing, became just as widely deployed as its older brother, email. Smishing is a scam that uses SMS as the attack vector. The goal is to trick the victim into revealing account information, installing malware on their device, or paying a sum to the hackers.
Here, as above, fake information and urgency are tactics used to make the texts appear to be from a reputable organization and something that the user must act upon immediately.
This is different from bulk SMS messaging, also known as mass texting, which is a legitimate way for firms, organizations, media companies, and financial institutions to reach a wide customer base with time-sensitive alerts and notifications to subscribers.
Smishing examples
Often considered a social engineering attack, smishing intends to exploit people and our hardwired vulnerabilities: trusting too easily, acting quickly, and wanting to be helpful.
In fact, while working on this piece, I was actually sent an SMS that has all the hallmarks of a well-crafted SMS phishing attack. This will help explain how easy it is to fall victim to these sneaky attacks.
The SMS I received claims to be from the Bank of Ireland or "BOI," and everything looks legitimate enough. The spelling is correct, and I’ve received similar notifications from other businesses. So this isn't something I should be concerned about, right?

Well, I don't have an account with the Bank of Ireland, so if I clicked on this link, it's very likely that the link would have compromised my device or requested credentials. The other giveaway is that the link doesn't mention the Bank of Ireland. Instead, it references an unfamiliar domain.
How to defend against SMS phishing
With standard phishing via email, you can check the email headers and actually hover over the links so that you can see if they're safe. However, with SMS phishing, you don't have those options.
Here are some ways to defend yourself against smishing:
- Do click only the links you expect and can vet.
- Do contact the bank, agency, or organization that the SMS claims to be from.
- Do delete the SMS if you can't verify it.
- Do be vigilant because, like all social engineering attacks, they rely on the human element. It's a lot easier to hack people than hack computers or phones.
Remember, if something is too good to be true, it usually is. Bob from accounting won’t send you an Apple gift card via an email, and it’s unlikely that a financial institution will send you an SMS with an unfamiliar link to update your account details.
SMS phishing vs. legitimate SMS messages: How can I tell the difference?
Let’s conclude by quickly comparing a standard series of Twilio SMS messages and (to the right) a scam message claiming to be from the delivery company DHL.
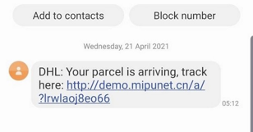
Consider that you received this message on your phone but weren’t expecting a delivery from DHL. Should you click and confirm? No. There are a few things in this image that should tip you off.
- The delivery was at 5 a.m. It's unlikely that you would receive a message that early from a provider.
- The URL is random and contains nothing about DHL in it.
- The URL is an HTTP (rather than HTTPS) site, which means all traffic is unencrypted. If you were to enter details on the site, the information could easily be harvested.
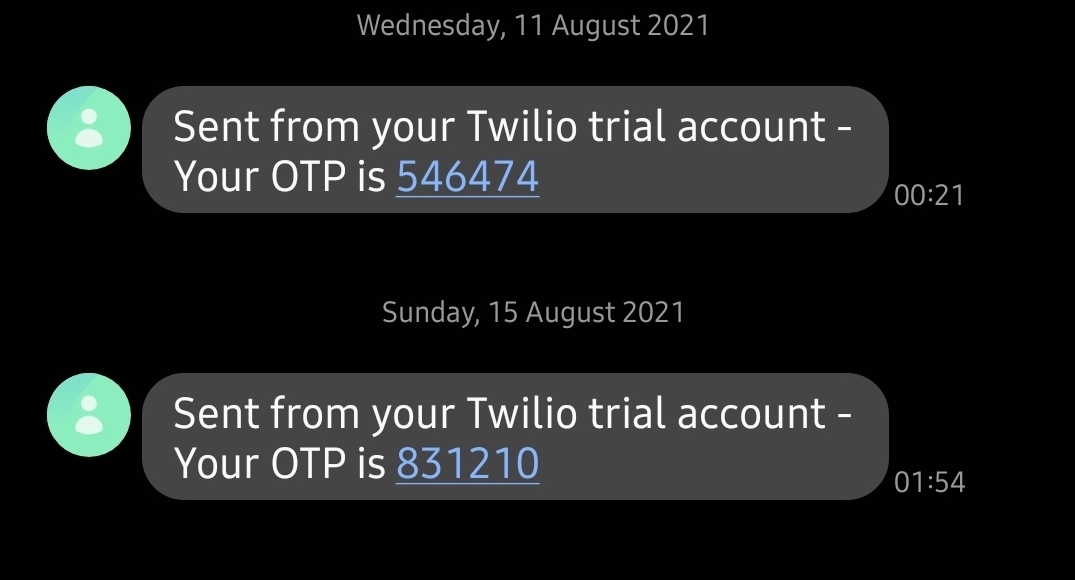
This is an example SMS from Twilio. The user received a verification code as they logged in, followed by another message to notify them of a password change.
- It provides something that you requested. In this case, a 2FA code and a notice of a password change.
- There is no attempt to get you to do something you didn’t already ask for.
- There are no random links.
- If you receive a bulk text message that uses Twilio, it will be from a service that you have signed up for (e.g., a supermarket promotion).
SMS phishing key takeaways
In a world that's more and more online than ever before, it's important to stay aware of how something as amazing as SMS can be used against you. While bulk SMS is a legitimate method of sending large quantities of texts to contacts, it's important to be wary of texts from unfamiliar companies.
To recap, the SMS phishing key takeaways are:
- Don't click links from texts you don't expect or brands you don't recognize.
- Do contact the bank, agency, or organization that the SMS claims to be from.
- Do delete the SMS if you can't verify it.
Like all social engineering attacks, the attackers rely on the human element, so be vigilant. It's a lot easier to hack people than to hack computers or phones. We hope the above will help you stay safe out there.
To set up bulk sending for your business, check out Twilio’s Programmable Messaging API and use the resources below to get started.
Related Posts
Related Resources
Twilio Docs
From APIs to SDKs to sample apps
API reference documentation, SDKs, helper libraries, quickstarts, and tutorials for your language and platform.
Resource Center
The latest ebooks, industry reports, and webinars
Learn from customer engagement experts to improve your own communication.
Ahoy
Twilio's developer community hub
Best practices, code samples, and inspiration to build communications and digital engagement experiences.